How to block Denial of Service (DoS) with null route
This article is described how I find out the Denial of Service (DoS) IP and null route it, to solve the high load issue on my server.
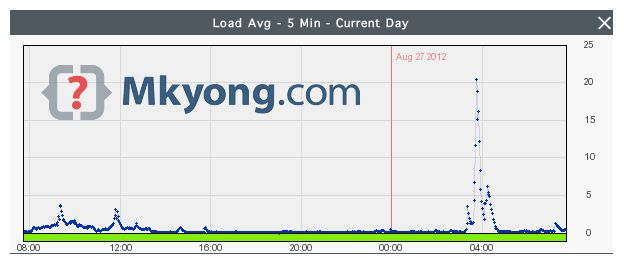
1. High Load
Recently, the server has hit an abnormally high load, CPU usage hits, average 15-20%.
#top
load average: 15.08, 18.30, 20.63
2. Who is Connected?
Not sure if this a DOS attack, or just a single IP abuse the connection? Issue following command to list all the IP addresses connected to my server.
#netstat -tn 2>/dev/null | grep :80 | awk '{print $5}' | cut -d: -f1 | sort | uniq -c | sort -nr | head
215 122.163.226.243
189 114.198.236.100
156 120.63.179.245
38 141.0.9.20
37 49.248.0.2
37 153.100.131.12
31 223.62.169.73
30 65.248.100.253
29 203.112.82.128
29 182.19.66.187
Below 3 IPs are taking 150+ connections, which is really abnormal, what are they trying to do?
215 122.163.226.243
189 114.198.236.100
156 120.63.179.245
P.S Google above IPs, 2 are from India, 1 from Pakistan.
3. null route
I believed above 3 IPs are the root cause of the high load issue, let null route those IPs, so that all incoming connections from those 3 IPs will be dropped or ignored.
null route command
route add 122.163.226.243 gw 127.0.0.1 lo
route add 114.198.236.100 gw 127.0.0.1 lo
route add 120.63.179.245 gw 127.0.0.1 lo
You can also use following command to null route the IPs, both are doing the same thing.
route add -host 122.163.226.243 reject
route add -host 114.198.236.100 reject
route add -host 120.63.179.245 reject
Uses netstat -nr to display all the routes, to make sure it is added into the route table.
# netstat -nr
Kernel IP routing table
Destination Gateway Genmask Flags MSS Window irtt Iface
114.198.236.100 127.0.0.1 255.255.255.255 UGH 0 0 0 lo
120.63.179.245 127.0.0.1 255.255.255.255 UGH 0 0 0 lo
122.163.226.243 127.0.0.1 255.255.255.255 UGH 0 0 0 lo
Done, wait a few seconds, and check the server load again, it’s back to normal now.
#top
load average: 1.08, 5.30, 30.63
Check all connected IP again, those attacker’s IPs are gone:
#netstat -tn 2>/dev/null | grep :80 | awk '{print $5}' | cut -d: -f1 | sort | uniq -c | sort -nr | head
40 141.0.9.20
37 49.248.0.2
36 153.100.131.12
31 223.62.169.73
25 65.248.100.253
29 203.112.82.128
29 182.19.66.187
38 142.0.9.20
28 141.121.9.20
38 141.0.9.201
Done.
4. Delete null route
To delete existing null route IPs, uses route delete.
route delete 122.163.226.243
route delete 114.198.236.100
route delete 120.63.179.245
To prevent Denial of Service (DoS), try setup CSF and configure the CT_LIMIT to limit the number of connections from IP to access server.
what if i would like add them permanently in my route file ….what would be syntax then
I really like this, it is a very clear and has concise execution. Do you know of any way to possibly do this from within the spring platform itself?
Thank you for this wonderful and clear instruction how to null ddos attackers. Good job!
absolutely brilliant! I’ll have to remember how to get to this page when I’ll need it…
This is wonderful idea. Very simple to implement in a script. In my case, my http servers are behind a F5 load balancer. Thus, connections are established, at operating system level, from the load balancer and not from the real client. Is there any way to get the real client IP with netstat command?
BR
Sorry, I’m not the expert in system admin.
My method may not apply on your case, my advice is implement firewall in front of your F5 load balancer, because load balancer is the entry point. Do consult with your system admin.